In March 2026, a Maryland wholesaler was charged with diverting 28,000 bottles of HIV medications purchased on the street, relabeling them with forged certificates, and reselling them to legitimate pharmacies. One patient received the wrong medication and lost consciousness within 24 hours. That’s why product authentication is so important in pharma.
This case represents a fundamental failure in pharmaceutical supply chain security: visual inspection and serial number verification could not distinguish diverted drugs from legitimate products. The bottles looked authentic. The serial numbers existed in databases. The forged certificates passed inspection.
What was missing? Item-level product authentication that proves, cryptographically, that the specific physical product being dispensed is genuine, not diverted, and authorized for that distribution channel.
This article explores why counterfeit and diverted pharmaceuticals continue to infiltrate legitimate supply chains, why traditional anti-counterfeiting solutions fail to stop them, and how cryptographic product authentication provides unforgeable verification at every supply chain touchpoint.
The Scale of Pharmaceutical Counterfeiting: 200,000+ Deaths Annually
The World Health Organization estimates that counterfeit and substandard pharmaceuticals cause approximately 200,000 deaths annually, with the majority occurring in developing nations where regulatory oversight is limited.
However, pharmaceutical diversion and counterfeiting are not confined to international markets. Recent cases in the United States demonstrate sophisticated infiltration of the legitimate supply chain:
$92 million HIV drug diversion (2026): 28,000 bottles of HIV medications were diverted from street purchases, relabeled with forged documentation, and sold to pharmacies across multiple states.
Counterfeit GLP-1 epidemic (2025-2026): Europol Operation SHIELD VI seized €33 million ($38.6 million) in counterfeit medicines, with fake semaglutide and tirzepatide representing the fastest-growing category. Maryland poison control centers reported a 1,500% increase in adverse events from compounded and counterfeit GLP-1 medications.
Fake Mounjaro KwikPens (UK, 2026): Sophisticated counterfeits containing tirzepatide but manufactured under unknown conditions—raising sterility and contamination concerns—were dispensed by a private clinic. The fakes were detected only after mechanical failures (detaching dose knobs) prompted investigation.
Counterfeit Ozempic (2025): FDA and international authorities continue to seize counterfeit semaglutide products entering both legitimate pharmacies and grey market distribution channels.
These cases share a common pattern: visual inspection, serial number verification, and documentation review failed to detect counterfeits or diverted products until patient harm occurred.
Why Traditional Pharmaceutical Supply Chain Security Fails
The pharmaceutical industry operates under some of the most stringent regulatory requirements globally, including the Drug Supply Chain Security Act (DSCSA) in the United States and the Falsified Medicines Directive (FMD) in the European Union. Despite these frameworks, counterfeit and diverted drugs continue to enter distribution.
Serialization Tracks Movement, Not Authenticity
DSCSA requires pharmaceutical manufacturers to serialize products and track their movement through the supply chain. This creates an auditable record of custody—where products moved and when—but it cannot verify that the physical product authentication is genuine.
Serial numbers can be:
- Copied from legitimate products onto counterfeits
- Transferred when drugs are repackaged (as in the HIV diversion case)
- Registered in databases for products that never reached legitimate distribution
Serialization answers “where did this serial number go?” but cannot answer “is the physical item I’m holding genuine?”
Visual Inspection Cannot Scale or Verify
Pharmaceutical packaging has become increasingly sophisticated, with holograms, tamper-evident seals, and special inks designed to prevent counterfeiting. However, sophisticated counterfeiters replicate these features with near-perfect accuracy.
More critically, visual inspection requires human verification at scale. In high-volume pharmaceutical distribution centers processing thousands of SKUs daily, relying on visual authentication is operationally unfeasible and produces inconsistent results.
Return Fraud Exploits Authentication Gaps
The rise of pharmaceutical return fraud—where customers return diverted, expired, or counterfeit products for refund or replacement—represents a growing vulnerability. When products return through reverse logistics, verification typically consists of:
- Visual packaging inspection (can be replicated)
- Serial number lookup (can be transferred)
- Expiration date check (can be relabeled)
Without item-level authentication at return intake, counterfeit and diverted products re-enter inventory, continuing the cycle of infiltration.
Grey Market Diversion Remains Invisible
Grey market diversion—where authentic products are purchased in one market and resold in unauthorized channels—undermines pricing strategies, violates distribution agreements, and creates compliance risks. Traditional supply chain security cannot distinguish between authorized and diverted authentic products because both are legitimate manufacturing outputs.
How Cryptographic Product Authentication Works in Pharmaceuticals
Cryptographic product authentication solves the fundamental problem that undermines serialization and visual security: it proves the specific physical item being verified is genuine, not merely that a valid serial number exists somewhere in a database.
The Technology: Secure NFC with Cryptographic Challenge-Response
XenTag’s pharmaceutical authentication uses NTAG 424 DNA chips—secure NFC silicon rated to EAL4+ security standards, the same certification used in payment cards and passports—embedded into drug packaging or labels.
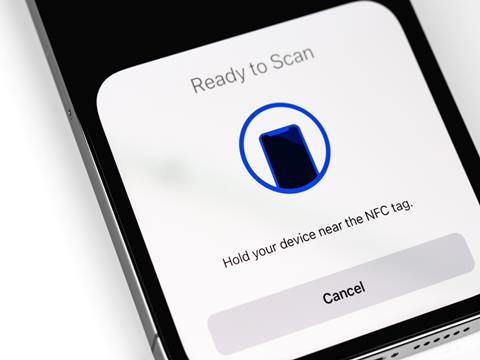
The authentication process:
- Challenge Generation: A smartphone or verification scanner sends a random cryptographic challenge to the NFC tag on the pharmaceutical product.
- Secure Response: The chip uses its internal cryptographic key—which never leaves the secure silicon—to generate a unique response to that specific challenge.
- Verification: The system validates the response. If correct, the product is authenticated. If incorrect or absent, the product fails verification.
This challenge-response protocol means every authentication is unique. Even if a counterfeiter intercepts a valid authentication exchange, they cannot use it—the next verification requires a different challenge and response.
Why Cryptographic Keys Cannot Be Cloned
Unlike serial numbers that can be copied or visual features that can be photographed, cryptographic keys stored in secure NFC chips cannot be extracted without destroying the chip. Tamper detection mechanisms erase secure memory if physical access is attempted.
Counterfeiters cannot:
- Copy the NFC tag (each contains unique cryptographic keys)
- Transfer the tag to fake products (tamper detection breaks authentication)
- Replay previous authentications (each requires a new challenge-response)
This creates unforgeable item-level proof.
Integration with DSCSA Compliance
Cryptographic authentication complements existing DSCSA serialization requirements rather than replacing them. While serialization tracks movement, authentication verifies authenticity:
DSCSA serialization: Records where products moved through the supply chain
Cryptographic authentication: Proves the physical product is genuine at each handoff
Together, these create a complete verification system: knowing both where a product moved and that each physical item at each step is authentic.
Product Traceability Solutions for Pharmaceutical Supply Chains
Effective pharmaceutical supply chain security requires visibility from manufacturing through patient dispensing, with verification at every handoff.
Manufacturing: Establishing Digital Identity
XenTag labels are applied during pharmaceutical manufacturing, creating a cryptographic binding between the physical product and its digital identity. This occurs before products enter distribution, establishing a verified chain of custody from first existence.
For pharmaceutical manufacturers, this means:
Batch-level tracking: Each product links to manufacturing batch, production date, facility location, and quality control records.
Serialization integration: Cryptographic authentication operates alongside DSCSA serialization, adding unforgeable verification to existing tracking.
Tamper detection: Physical manipulation of packaging breaks the cryptographic binding, making tampering immediately detectable.
Quality event recording: Authentication failures trigger investigation workflows for potential counterfeits or diversion.
Distribution: Supply Chain Handoff Verification
As pharmaceuticals move from manufacturer to distributor to pharmacy, each handoff creates an authentication event logged on immutable blockchain ledgers.
This provides:
Custody verification: Each party authenticates products at receipt, confirming legitimate transfer
Unauthorized channel detection: Products authenticating outside approved distribution trigger alerts
Diversion identification: Grey market products fail authentication when they appear in unauthorized channels
Audit trails: Unforgeable records for regulatory compliance and investigation
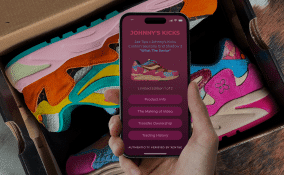
Dispensing: Patient-Level Authentication
When pharmacies dispense medication, authentication at the point of sale provides final verification before products reach patients.
Real-time verification: Pharmacists tap products with smartphones (no app required) for sub-3-second authentication
Patient safety: Counterfeit or diverted products fail authentication before dispensing
Recall efficiency: Products affected by recalls are flagged during authentication, preventing dispensing
Grey market detection: Diverted products attempting re-entry into legitimate channels are identified at intake
Returns: Reverse Logistics Verification
Pharmaceutical returns—whether from pharmacies, distributors, or patients—require verification before re-entering inventory or triggering refunds.
Return fraud prevention: Verify products are genuine before authorizing refunds or replacements
Counterfeit detection: Fake products attempting entry through returns are flagged at intake
Diversion identification: Street-purchased products relabeled for return (as in the HIV case) fail authentication
Duplicate claim detection: Products previously returned cannot be authenticated again
This reverse logistics verification closes the loop that enables return fraud and counterfeit infiltration.
Anti-Counterfeiting Solutions That Address Pharmaceutical-Specific Risks
Pharmaceutical products face unique counterfeiting and diversion risks that differ from other industries.
High-Value Targets with Life-or-Death Consequences
Pharmaceuticals represent some of the highest-value targets for counterfeiting due to:
Premium pricing: Specialty medications, oncology drugs, and biologics command prices that create massive profit incentives for counterfeiters.
Inelastic demand: Patients requiring life-saving medications will pay premium prices or seek grey market alternatives when legitimate products are unaffordable or unavailable.
Difficult verification: Most patients and even healthcare professionals cannot visually distinguish authentic pharmaceuticals from sophisticated counterfeits.
Catastrophic patient harm: Unlike counterfeit luxury goods or cosmetics, fake pharmaceuticals kill. Every authentication failure represents potential patient death.
Regulatory Compliance Requirements
Pharmaceutical manufacturers must navigate complex regulatory requirements:
DSCSA (United States): Product and case serialization, verification at each supply chain handoff, interoperable electronic tracing by 2023 (extended)
FMD (European Union): Unique identifiers and anti-tampering devices on prescription medications
GDP (Good Distribution Practice): Quality assurance throughout pharmaceutical supply chains
21 CFR Part 11: Electronic records and electronic signatures compliance for digital systems
Cryptographic authentication integrates with these requirements, providing the verification layer that serialization alone cannot deliver.
Cold Chain and Specialty Medications
Temperature-sensitive biologics, vaccines, and specialty medications require not only authentication but environmental monitoring throughout distribution.
XenTag’s platform can integrate with cold chain monitoring systems, linking authentication events with temperature excursion alerts. This ensures that:
- Products were maintained in proper storage conditions throughout distribution
- Temperature excursions are flagged during authentication
- Compromised medications cannot be dispensed even if technically “authentic.”
Supply Chain Security for Pharmaceutical Distribution Networks
Pharmaceutical distribution involves multiple parties—manufacturers, wholesalers, distributors, pharmacies, hospitals, and patients—each representing a potential point of counterfeit infiltration.
Wholesale Distribution Vulnerabilities
The Maryland HIV drug diversion case demonstrates how sophisticated actors exploit wholesale distribution:
- Street acquisition: Medications purchased from patients who sold their prescriptions
- Relabeling: Products repackaged with forged pedigree documentation
- Wholesale sale: Sold to distributors at below-market prices (creating an incentive to accept)
- Pharmacy distribution: Legitimate pharmacies unknowingly stocked diverted products
- Patient harm: Wrong medications dispensed, causing hospitalization
Cryptographic authentication would have stopped this at step 3: diverted products attempting wholesale authentication would fail because they had already authenticated at the original patient dispensing. The products could not prove a legitimate custody chain.
Online Pharmacy and Direct-to-Consumer Risks
The rise of online pharmacies and direct-to-consumer medication sales creates additional vulnerabilities:
Unregulated online sellers: Websites claiming to sell prescription medications without prescriptions
Compounding pharmacies: Legitimate and illegitimate compounders producing medications of unknown quality
International imports: Medications purchased from non-FDA-approved international sources
Social media sales: Direct sales of controlled substances and specialty medications via social platforms
Consumers purchasing from these channels have no reliable way to verify authenticity. Item-level authentication accessible via smartphone provides a verification mechanism before consumption.
Hospital and Institutional Settings
Healthcare institutions face unique risks:
Group purchasing: Bulk purchasing creates price pressure that can incentivize grey market sourcing
Pharmacy compounding: In-house compounding of medications requires verification of source ingredients
Clinical trials: Investigational drugs require strict custody verification
Controlled substances: Diversion of high-value controlled substances for resale
Authentication at institutional intake ensures only genuine products enter hospital pharmacies and clinical settings.
The Business Case for Pharmaceutical Authentication
Beyond patient safety and regulatory compliance, pharmaceutical product authentication creates measurable business value.
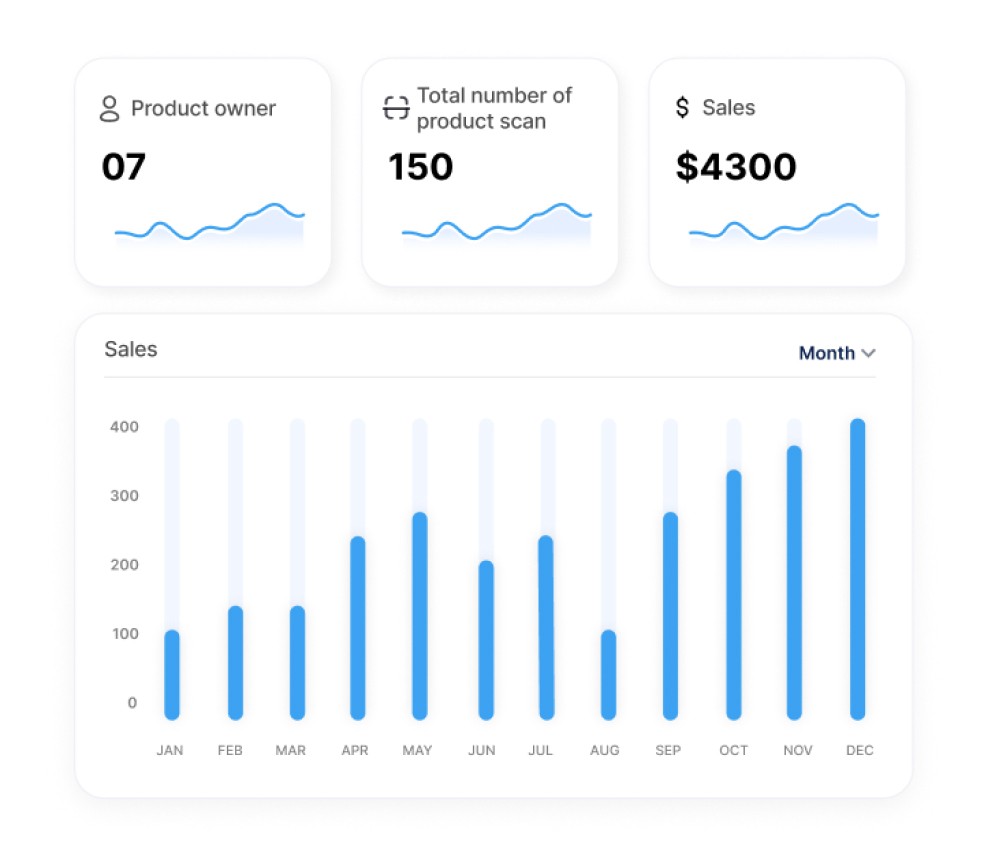
Return Fraud Prevention
Pharmaceutical return fraud manifests in several ways:
Counterfeit swaps: Patients purchase genuine medication, replace it with counterfeits, and return for a refund
Expired product relabeling: Street-purchased expired medications relabeled and returned as current stock
Warranty abuse: Grey market products returned through authorized channels for replacement
Double-dipping: Same product returned multiple times through different channels
Cryptographic authentication at return intake verifies authenticity before refund authorization, eliminating these fraud vectors.
Industry data shows pharmaceutical return fraud costs manufacturers and distributors approximately $8-12 billion annually. Item-level authentication at intake can reduce this by 80-90% by preventing fraudulent returns from entering refund workflows.
Grey Market Detection and Pricing Integrity
Pharmaceutical manufacturers establish different pricing for different markets (international vs. domestic, institutional vs. retail, etc.). Grey market diversion—where products are purchased in low-price markets and resold in high-price markets—undermines this pricing strategy.
Authentication events create visibility into distribution patterns:
Expected channels: Products authenticate in authorized distribution only
Diversion alerts: Products authenticating outside approved channels trigger investigation
Pricing enforcement: Contractual compliance with distribution agreements becomes verifiable
Market segmentation: Different products or formulations can be limited to specific markets
This visibility allows pharmaceutical companies to identify and address diversion before it becomes systematic.
Recall Efficiency and Patient Safety
When pharmaceutical products are recalled due to contamination, manufacturing defects, or adverse events, reaching all affected products quickly is critical to patient safety.
Traditional recalls rely on distributors and pharmacies checking batch numbers against recall lists—a manual, error-prone process with incomplete coverage.
Cryptographic authentication enables automated recall enforcement:
- Recalled products are flagged in the authentication database
- Any attempt to authenticate recalled products generates failure + alert
- Pharmacies cannot dispense flagged products even if batch numbers were missed
- Patients can verify products before use, providing a final safety check
This transforms recalls from “notify and hope” to “verify and prevent.”
XenTag’s Approach to Pharmaceutical Product Authentication
XenTag provides a cryptographic product authentication specifically designed for pharmaceutical manufacturers facing counterfeiting, diversion, and return fraud pressures.
What Makes Pharmaceutical Authentication Different
NTAG 424 DNA secure silicon: EAL4+ certified cryptographic chips, same security standard as payment cards
No-app verification: Native smartphone NFC support (2+ billion devices) enables tap-to-verify without downloads
DSCSA integration: Works alongside existing serialization infrastructure, adding authentication to tracking
Tamper detection: Physical manipulation breaks the cryptographic binding, making the package opening detectable
Blockchain immutability: Authentication events recorded on unforgeable ledgers for regulatory compliance
Sub-3-second verification: Real-time authentication without operational bottlenecks
Cold chain integration: Links authentication with environmental monitoring for temperature-sensitive products
Implementation for Pharmaceutical Manufacturers
XenTag works with pharmaceutical manufacturers, contract packagers (CMOs), and third-party logistics providers (3PLs) to integrate authentication:
- Tag encoding: Each product receives unique cryptographic keys during packaging, establishing a digital identity
- Label integration: Tags embed into existing pharmaceutical labels or packaging—no packaging redesign required
- Serialization integration: Authentication operates alongside DSCSA serialization systems via API integration
- Distribution verification: Wholesalers, distributors, and pharmacies authenticate at receipt using smartphones
- Dispensing authentication: Pharmacists verify products before dispensing to patients
- Return verification: Products are authenticated at return intake before refund or replacement authorization