The counterfeit cosmetics market reached $76.5 billion in 2025, accounting for 9% of all beauty product sales globally. For legitimate cosmetics brands, this represents more than lost revenue; it means damaged reputations, safety risks to consumers, and an erosion of customer trust that can take years to rebuild.
As e-commerce continues to dominate beauty product sales, traditional anti-counterfeiting solutions like visual inspection, holograms, and QR codes have proven insufficient. Counterfeiters replicate packaging with increasing sophistication, and once fake products enter distribution channels, distinguishing authentic cosmetics from counterfeits becomes nearly impossible.
This article explores the scale of counterfeit cosmetics, why conventional brand protection solutions fail in modern e-commerce environments, and how cryptographic product authentication provides a new standard for stopping fake beauty products before they reach consumers.
The Scale of Counterfeit Cosmetics: $76.5 Billion in Annual Fraud
According to the National Retail Federation’s 2025 Retail Returns Landscape report, total retail returns reached $850 billion, with 9% classified as fraudulent. For the cosmetics industry specifically, this fraud manifests in several ways:
Counterfeit product swaps: Retailers report a 64% increase in returns where customers swap authentic cosmetics for counterfeit versions, then claim refunds for the genuine products they keep.
Empty box returns: Beauty retailers experienced a 65% increase in “empty box” or partial returns, often involving counterfeit replacements.
Grey market diversion: Authentic products purchased in one market are diverted to unauthorized channels, undermining brand-authorized distribution and pricing strategies.
Online marketplace infiltration: A 2026 study from Partnership for Safe Medicines found that counterfeit beauty products now appear on major e-commerce platforms within 48 hours of authentic product launches, exploiting gaps in marketplace verification systems.
The impact extends beyond financial losses. The World Health Organization estimates that counterfeit cosmetics containing toxic substances like lead, arsenic, and mercury cause approximately 1 million adverse health incidents annually, with severe cases resulting in chemical burns, allergic reactions, and long-term skin damage.
For cosmetics brands, the reputation damage is immediate. Research shows that 52% of consumers lose trust in a brand after purchasing a counterfeit product, even when the brand had no control over the fake entering distribution.
Why Traditional Anti-Counterfeiting Solutions Fail in E-Commerce
Conventional brand protection solutions were designed for physical retail environments where products could be visually inspected before sale. These methods fail in modern supply chains for several critical reasons:
Visual Authentication Cannot Scale
Holograms, special inks, and embossed labels require human inspection to verify. In high-volume e-commerce fulfillment centers processing thousands of SKUs per hour, visual verification is operationally unfeasible. More importantly, sophisticated counterfeiters now replicate these visual security features with near-perfect accuracy.
QR Codes Can Be Copied
QR codes are often marketed as anti-counterfeiting packaging solutions, but they present a fundamental security flaw: they can be photographed and reproduced. Once a legitimate QR code is scanned, fraudsters can print identical codes on counterfeit packaging. The verification system has no way to distinguish between the authentic product and the copy bearing the same code.
Serialization Tracks Movement, Not Authenticity
Supply chain serialization systems like those required by pharmaceutical regulations track where products move, but they cannot verify that the physical item being scanned is genuine. Serial numbers can be copied or transferred to counterfeit products, creating a false authentication record.
Return Fraud Exploits Authentication Gaps
The rise of e-commerce returns has created a new vulnerability. When customers return cosmetic products, retailers typically verify the serial number or visual appearance, but cannot confirm the physical product is authentic. This gap enables counterfeit swaps, where genuine products are kept, and fakes are returned in their place.
Traditional methods lack one critical capability: the ability to verify that the specific physical item being authenticated is genuine, not a cleverly packaged counterfeit bearing copied security features.
How Cryptographic Product Authentication Works
Cryptographic authentication solves the replicability problem that undermines QR codes and visual security features. Instead of relying on something that can be photographed or reproduced, cryptographic solutions use secure hardware that performs mathematical operations impossible to clone.
The Technology Behind Cryptographic NFC
XenTag’s anti-counterfeiting solutions use NTAG 424 DNA chips—secure NFC silicon rated to EAL4+ security standards—embedded into product labels or packaging. These chips contain cryptographic keys that never leave the secure hardware.
When a cosmetics product is authenticated, the following process occurs:
- Challenge Generation: The verification system (a smartphone or scanner) sends a random cryptographic challenge to the NFC tag.
- Secure Response: The chip uses its internal cryptographic key to generate a unique response to that specific challenge. This operation happens inside the secure silicon—the key itself is never transmitted.
- Verification: The system validates the response against expected cryptographic signatures. If the response is correct, the product is authenticated.
This challenge-response protocol means every authentication is unique. Even if a counterfeiter intercepts a valid authentication exchange, they cannot replay it—the next authentication requires a different challenge and response.
Why This Cannot Be Cloned
Unlike QR codes or visual features, cryptographic keys cannot be extracted from secure NFC chips without destroying the chip itself. Attempting to physically access the key triggers tamper detection mechanisms that erase the secure memory.
Counterfeiters cannot:
- Copy the NFC tag (each tag has unique cryptographic keys)
- Photograph or screenshot the authentication (each scan requires a new challenge-response)
- Transfer the tag to fake products (tamper detection breaks authentication when removed)
This creates unforgeable item-level proof that the specific physical product being verified is genuine.
The impact of counterfeit cosmetics on legitimate brands
Statistically, one in every two customers in the United States loses their faith in a brand if they happen to purchase a counterfeit version of a cosmetic product. The unchecked rise of fake cosmetic products has cost legitimate brands revenue, but also their reputation and trust in their brand.
Anti-Counterfeiting Packaging: Item-Level Verification for Beauty Brands
Effective anti-counterfeiting solutions for packaging integrate authentication into the product itself rather than relying on external verification layers that can be circumvented.
Embedding Authentication at Manufacturing
XenTag labels are applied during the manufacturing process, creating a cryptographic binding between the physical product and its digital identity. This occurs before products enter distribution, establishing a verified chain of custody from the first moment of existence.
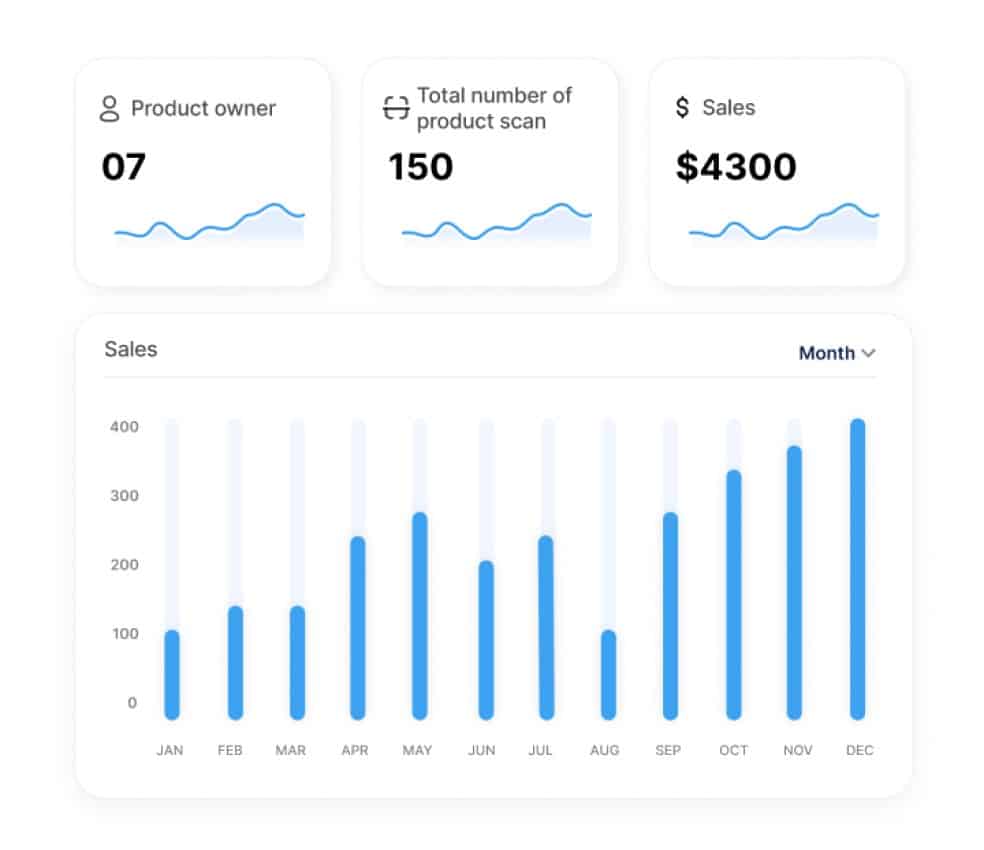
For cosmetics brands, this means:
Manufacture verification: Each product receives a unique digital identity at production, recorded with batch information, production date, and facility location.
Supply chain handoffs: Authentication events are logged as products move from manufacturer to distributor to retailer, creating an auditable record of custody.
Consumer verification: End customers can tap the product with their smartphone—no app download required—to verify authenticity in under 3 seconds.
Return verification: When products return for refund or warranty, retailers authenticate at intake to confirm the physical item is genuine before authorizing replacement.
The No-App Advantage
Earlier product authentication solutions required consumers to download proprietary apps, creating significant friction. XenTag uses native NFC functionality built into modern smartphones, over 2 billion devices globally, enabling tap-to-verify authentication without downloads.
This removes the primary barrier to consumer adoption while maintaining the security of cryptographic verification.
Brand Protection Solutions That Scale with Your Business
Small and mid-sized cosmetics brands face a disproportionate impact from counterfeiting. While major beauty corporations like Estée Lauder and L’Oréal maintain dedicated anti-counterfeiting task forces, emerging brands lack the resources to pursue counterfeiters through legal channels.
Cryptographic product authentication levels the playing field by making enterprise-grade brand protection accessible at any scale.
Cost-Effective Implementation
Traditional anti-counterfeiting solutions required significant upfront investment in proprietary systems, custom packaging, and ongoing monitoring infrastructure. Modern cryptographic authentication operates on a per-unit cost model that scales with production volume.
For cosmetics brands producing 10,000 to 100,000 units annually, item-level authentication becomes economically viable without enterprise-level capital expenditure.
Integration with Existing Operations
XenTag labels integrate into standard cosmetics packaging and labeling workflows without requiring specialized application equipment. Labels can be applied manually for small batches or integrated into automated labeling systems for high-volume production.
This operational flexibility allows brands to implement authentication incrementally, starting with high-value product lines or markets with elevated counterfeiting risk, then expanding as business needs evolve.
Multi-Use Case Value
Beyond anti-counterfeiting, cryptographic authentication enables additional use cases that create ROI:
Return fraud prevention: Verify authenticity at return intake, eliminating counterfeit swaps before refunds are authorized.
Grey market detection: Track which distribution channels products are authenticated through, identifying unauthorized resellers.
Warranty verification: Confirm products are genuine and within the warranty period before approving service claims.
Resale authentication: Enable secondhand market verification, protecting brand reputation in pre-owned channels.
Sustainability tracking: Record recycling or take-back program participation for circular economy initiatives.
This multi-use approach transforms authentication from a defensive cost into a strategic capability that improves operations across the product lifecycle.
XenTag’s Approach to Cosmetics Authentication
XenTag provides a cryptographic product authentication specifically designed for cosmetics brands facing counterfeiting pressures in e-commerce and international distribution.
What Makes XenTag Different
Cryptographic security: TAG with cryptographic codification and certification, the same security standard used in payment cards and passports.
No-app verification: Native smartphone NFC support means consumers verify authenticity by tapping their phone, no download required.
Tamper detection: Physical manipulation breaks the cryptographic binding, making tag removal or transfer immediately detectable.
Blockchain immutability: Authentication events are recorded on immutable ledgers, creating unforgeable audit trails for regulatory compliance and supply chain visibility.
Sub-3-second verification: Authentication completes in under 3 seconds, enabling real-time verification at scale without operational bottlenecks.
Implementation for Beauty Brands
XenTag works with cosmetics manufacturers, contract packagers, and brands to integrate authentication into production workflows:
- Tag encoding: Each product receives unique cryptographic keys during manufacturing, establishing a digital identity.
- Label application: Tags are embedded into existing packaging—product labels, boxes, or tamper-evident seals—without requiring packaging redesign.
- Supply chain tracking: Authentication events log as products move through distribution, creating custody records.
- Consumer verification: Customers tap products with smartphones to verify authenticity before purchase or use.
- Return authentication: Retailers verify returned products at intake, stopping counterfeit swaps before refund authorization.
Pilot Programs for Emerging Brands
XenTag offers pilot programs allowing cosmetics brands to test authentication on limited product runs—typically 500 to 2,000 units—before full deployment. Pilots run for 60 to 90 days and include success criteria like return fraud reduction, grey market detection, or consumer engagement metrics.
This pilot-first approach allows brands to validate ROI and operational fit before committing to enterprise-scale implementation.