The internet was built for information exchange. Payments were bolted on later.
For decades, commerce has required layers: logins, subscriptions, coupons, checkout pages, loyalty databases, and payment gateways. Friction has been normalized, and that is about to change with smart packaging.
With the emergence of x402, the long-dormant HTTP 402 “Payment Required” status code is being transformed into a machine-native payment protocol. Payment becomes part of the internet’s core request-response cycle. A resource can request payment, receive settlement, and grant access—all within a single, automated flow.
This shift does more than simplify checkout. It fundamentally changes how consumers interact with products. When smart packaging with secure NFC tags enables cryptographic product authentication, and x402 enables native payments, products stop being static goods.
They become economic actors.
From Smart Labels to Economic Endpoints
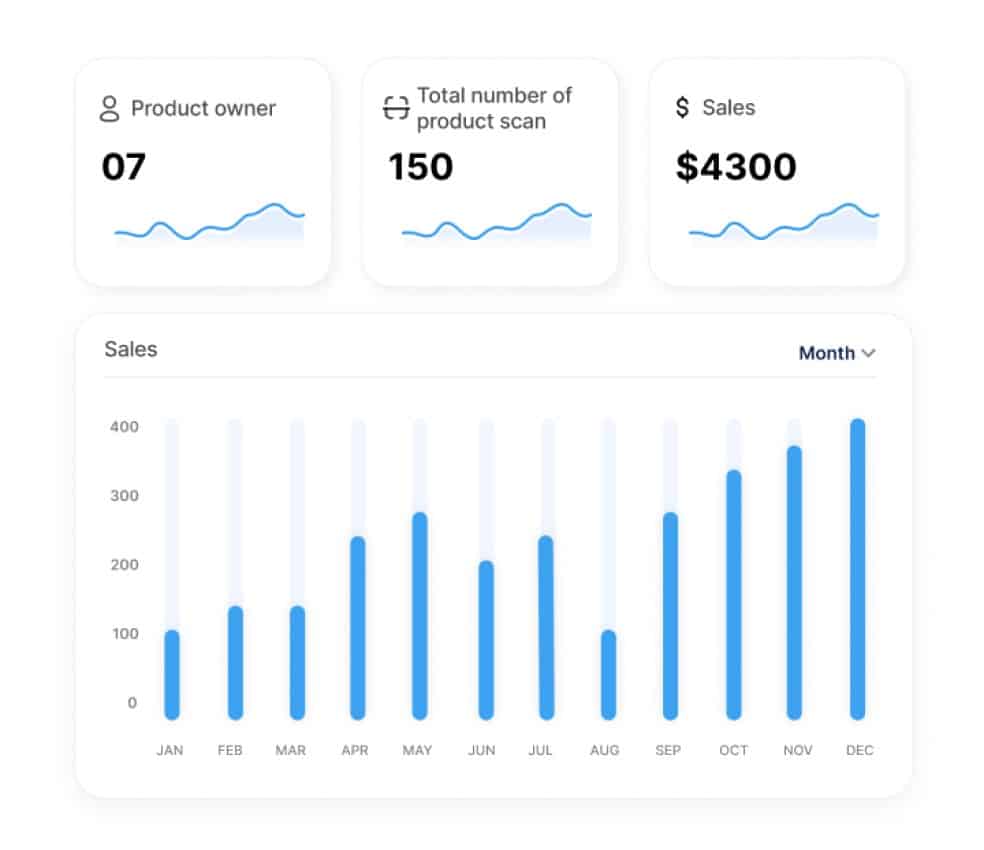
Smart labels powered by product authentication technology create a new foundation for commerce. XenTag embeds a secure, unclonable identity into each product using anti-counterfeiting solutions built on cryptographic hardware. When you first interact, the system automatically creates a custodial Algorand wallet for you. Every purchased product is registered in that wallet.
This creates a new primitive. Each physical product is now:
→ Cryptographically unique
→ Wallet-aware
→ Blockchain-linked
→ Event-trigger capable
When you combine smart packaging with x402-enabled payment flows, something powerful happens: every product becomes capable of initiating, receiving, and settling micropayments securely and transparently.
Six Ways Smart Packaging Transforms Commerce
1. Loyalty Becomes Programmable and Instant
Traditional loyalty systems operate as siloed databases. Points live in backend systems. Redemption requires manual checkout steps. Fraud and reconciliation are constant challenges.
With smart labels:
- Loyalty tokens are issued as Algorand Standard Assets
- Credited directly to the consumer’s custodial wallet
- Verifiable, auditable, global, and programmable
With x402:
- Redemption happens inside the HTTP interaction
- The product or website returns a 402 Payment Required response
- The wallet pays using loyalty tokens
- Access or a discount is granted instantly
No coupon codes, no waiting for backend validation, no reconciliation cycles.
Loyalty transforms from a marketing abstraction into a micro-currency native to the product ecosystem.
2. Discounts Become Atomic and Trustless
Imagine a consumer tapping a smart packaging product and accessing a refill page. The server responds: “Redeem 100 loyalty tokens for a $10 discount?”
The consumer’s wallet executes the transaction. The discount applies instantly. The blockchain records the settlement.
Because the payment is on-chain:
→ It cannot be duplicated
→ It cannot be forged
→ It cannot be retroactively altered
Discounting becomes atomic and trustless—settled in seconds.
3. Supply Chain Security Through Real-Time Product Intelligence
Product traceability solutions built on smart labels generate authenticated product lifecycle data:
→ Activation date
→ Usage intervals
→ Batch identity
→ Geographic movement (if opted-in)
Manufacturers gain real-time visibility into:
→ True product activation rates
→ Consumption patterns
→ Regional demand signals
→ Inventory velocity
This moves forecasting from probabilistic to event-driven. Supply chain security improves because products themselves become live data nodes feeding directly into supply chain systems.
The result:
- Lower overproduction
- Reduced stockouts
- Smarter distribution
- More accurate demand planning
Traditional inventory management relies on estimates and historical trends. Smart packaging generates authenticated event data at every consumer interaction, capturing activation timing, consumption location, and replacement frequency. This shifts forecasting from probabilistic models to real-time visibility.
Manufacturers can identify unexpected demand patterns, adjust distribution proactively, and prevent stockouts before they happen. The product traceability solutions move from “what we shipped” to “what consumers actually activated and used.”
4. Automatic Reordering Through Agentic Commerce
x402 was designed for autonomous, agent-driven transactions.
When a product is nearing depletion:
- The consumer taps the smart label
- Or an AI assistant detects usage cadence
- The reorder endpoint responds with a 402 payment requirement
- The wallet settles the payment instantly
- Fulfillment is triggered automatically
No cart, no subscription management, no manual checkout. The smart packaging itself becomes the reorder interface. For consumables, this eliminates friction while preserving consumer control. For manufacturers, it reduces churn and increases lifetime value.
5. The Product as a Direct Revenue Channel
Historically, sales channels have been external to the product: retail stores, ecommerce platforms, marketplaces.
With smart labels + x402, the product becomes:
→ A loyalty issuer
→ A discount engine
→ A reorder trigger
→ A micropayment processor
→ A direct fulfillment initiator
In effect, every unit sold becomes a persistent, blockchain-linked sales terminal in the hands of the consumer.
This collapses the boundary between:
- Marketing
- Commerce
- Fulfillment
- Loyalty
- Payments
They converge into a single programmable interaction layer enabled by anti-counterfeiting solutions that verify product authenticity at every transaction.
6. Secure Micropayments at Scale
Micropayments historically failed because card fees were too high, settlement was too slow, and infrastructure was too fragmented.
Algorand provides:
→ Low transaction costs
→ Deterministic finality
→ Native asset support
x402 provides:
→ Standardized payment negotiation at the HTTP level
→ Machine-readable payment requests
→ Seamless API integration
XenTag’s smart packaging provides:
→ Wallet auto-provisioning
→ Verified product authentication
→ Consumer ownership mapping
Together, they make it economically viable for products to handle payments measured in cents—or fractions of cents—in real time.
A New Era of Product Design: Smart Packaging as Infrastructure
We are entering a period where product design is no longer limited to materials, packaging aesthetics, and functional performance.
Instead, products will be designed with embedded economic logic.
A smart packaging product is not just an object. It is:
→ A programmable node
→ A wallet-linked asset
→ A loyalty engine
→ A data source
→ A fulfillment trigger
→ A micropayment endpoint
When combined with x402, the consumer interaction model changes from “scan and view” to “tap and transact.”
The product becomes a living interface between manufacturer and consumer—secure, transparent, and autonomous.
The Strategic Implication for Brand Protection Solutions
For brands, this means:
→ Direct-to-consumer economics without platform dependency
→ Real-time loyalty issuance and redemption
→ Closed-loop inventory intelligence through product traceability solutions
→ Frictionless automatic reordering
→ Cryptographically secure micropayments
For consumers, this means:
→ Immediate rewards
→ Seamless discounts
→ Effortless reordering
→ Transparent ownership
→ Secure, low-friction transactions
The companies that embrace this shift will not simply digitize products. They will redesign products as economic participants in a programmable commerce network.
Anti-counterfeiting packaging evolves from passive protection to active commerce infrastructure. Supply chain security becomes real-time and product-driven. Brand protection solutions transform from defensive measures into revenue enablers.
Explore XenTag’s Smart Packaging Solutions
XenTag provides product authentication, anti-counterfeiting solutions, and smart labels that transform products into programmable commerce endpoints. Our secure NFC tags enable cryptographic verification, wallet integration, and x402-native micropayments.
Learn more about how smart packaging can create new revenue channels for your products: xentag.com/solutions/platform